Maximizing Service Defense: The Ultimate Overview to Electronic Security Solutions
In the fast-paced and ever-evolving landscape of organization safety, the reliance on electronic protection services has come to be vital for protecting valuable properties, private information, and keeping operational continuity. In this overview to electronic protection services, we will discover the newest trends, sophisticated innovations, and finest practices to strengthen your company against possible dangers and vulnerabilities.
Relevance of Electronic Safety And Security Solutions
When considering the security of assets and delicate details, the relevance of digital safety remedies can not be overemphasized. In today's interconnected globe, where cyber threats are regularly evolving and ending up being more advanced, organizations must prioritize carrying out durable electronic safety and security procedures to safeguard their data and operations. Digital protection solutions include a vast array of innovations and techniques designed to resist unauthorized gain access to, information violations, malware, and various other cyber hazards.
One of the essential advantages of digital protection solutions is their capability to supply real-time surveillance and risk discovery. BQT Electronic Security. Via tools like intrusion detection systems, firewall softwares, and protection information and event management (SIEM) systems, organizations can proactively determine and react to protection incidents before they intensify into significant violations. In addition, digital protection remedies assist make sure compliance with market regulations and standards, protecting organizations from possible lawful and monetary repercussions
Kinds of Electronic Safety And Security Systems
Offered the important significance of digital safety services in safeguarding services against cyber threats, it is important to discover the different kinds of digital safety and security systems readily available to boost protection and strength. One of one of the most typical sorts of digital safety and security systems is the firewall program, which serves as a barrier in between a company's inner network and outside networks, removing potentially hazardous information. Intrusion Discovery Equipment (IDS) are additionally essential, as they keep track of network traffic for dubious activity and sharp managers to potential dangers. In addition, companies usually depend on file encryption modern technologies to secure sensitive information both at remainder and in transit. Access control systems, including biometric viewers and keycard accessibility, help regulate entrance to physical areas and shield assets. Video monitoring systems play a duty in monitoring and recording activities within and around the facilities. By using a mix of these electronic safety systems, organizations can establish a robust defense versus numerous security risks.
Applying Accessibility Control Procedures
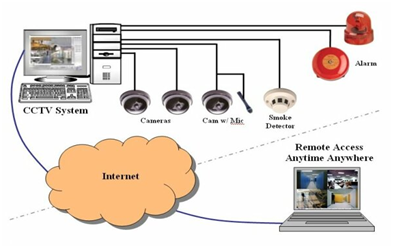
In addition, gain access to control about his measures can be incorporated with surveillance systems to check and tape-record people' activities within secured areas. This assimilation read this article improves security by providing an extensive introduction of that is accessing details locations at any provided time. Gain access to control systems can be configured to restrict gain access to based on time, place, or private credentials, allowing companies to customize safety and security protocols according to their particular needs.
Cybersecurity Best Practices
To improve overall protection position, implementing durable cybersecurity best methods is crucial in protecting electronic assets and information integrity. Carrying out routine safety audits and assessments assists identify weak points and locations for improvement.
Developing an extensive case reaction strategy enables swift and reliable reactions to protection breaches, lessening potential damage. Securing delicate data both in transit and at remainder gives an additional obstacle versus information breaches. Executing accessibility controls based on the principle of least opportunity restricts the exposure of vital systems and details to just those who require it for their functions. Routine back-ups of information ensure that in the event of a ransomware assault or information loss, essential information can be recuperated. Accepting an aggressive approach to cybersecurity with constant surveillance and threat intelligence assists identify and mitigate prospective threats before they intensify. By integrating these ideal techniques into cybersecurity techniques, services can strengthen their defenses against developing cyber threats.
Monitoring and Tracking Solutions

Video clip surveillance options offer remote tracking capacities, allowing licensed employees to keep an eye on the facilities also when off-site. Additionally, advanced functions like activity detection, facial recognition, and certificate plate recognition enhance the general protection posture of the company. Incorporating security systems with security system and accessibility control further enhances the safety framework, allowing an aggressive response to potential safety violations.
Conclusion
In conclusion, digital safety options are vital for taking full advantage of company protection. It is vital to spend in the best digital safety systems to guarantee the safety and protection of the company.